No is the time everyone makes resolutions to eat healthy, lose weight and exercise so why not make some related to your business?Here are a few recommendations from my area of expertise-
#1: Automate Repetitive I.T. Tasks.
Many tasks can be automated, from the very simple to the more complex. A great place to start is to make sure your servers and systems all run security updates, system patches, and antivirus/malware definitions automatically and apply them. Next up would be to find all the places where time is consumed moving files around or even duplicating effort entering data into multiple systems. With automated importing and exporting these redundant tasks can free up your time and make you more efficient.
#2: Invest in Customer Relationship Management (CRM) Software.
Turn your customer data into something you can use to help you become more efficient and to grow your business. So many companies store their customer data in spreadsheets or in files scattered across the office. Customer Relationship Management Software helps you manage your customer relationships and track not only their orders but also their interaction with you via phone, email or other means. With a few clicks you can find out who your most valuable customers are, which ones are consuming large amounts of your time and which ones are prospects for growth in the upcoming year. There are many packages on the market that can help you with this, ranging from off-the-shelf varieties that can suit most business needs and are available at your local office supply store to fully customizable one from big vendors such as Microsoft and Oracle. Take some time this New Year to read up more on CRM software and learn how it can be a valuable tool in managing your customers and your business.
#3: Back Up Your Data.
Backup, Backup, Backup. What would happen to your business come tomorrow if you woke up and found out that your computer with all your finances, customer information and invoices had died? All too often small businesses don’t back up their data and as a result their computers turn into ticking time bombs. Resolve in 2010 to make better use of backup software and other technology that helps keep you protected from the failure that will happen sooner or later.
#4: Install a Good Accounting Package.
2010 should be the year you stop using spreadsheets to track your finances and invest in a good accounting package. Spreadsheets are good for very small businesses, but the moment when you start growing you will find that you are being held back by their lack of ability to manage complex financial transactions. Another benefit you will receive from investing in a good accounting package is that tax time will be a breeze. Many accounting packages on the market today have modules that let you literally point, click and print your tax returns for your business! A good accounting package can pay for itself within weeks. Think how much more effectively you could run your business when you can get up in the morning and see, at-a-glance, how well your business is doing.
Last but not least...
#5: Bring In an I.T. Professional!
Your business is not I.T., so why invest your valuable time? The time spent making sure everything's backed up, up to date, running efficiently, malware scanned, clear of viruses, and so on should be done by an expert in that field. When your vehicle needs maintenance you go to a mechanic and when it's tax time you go to an accountant. Your business network and systems need the same attention.
So now it’s time for you to act.
Start by making an action plan to put in place now to guide you through the 2010.

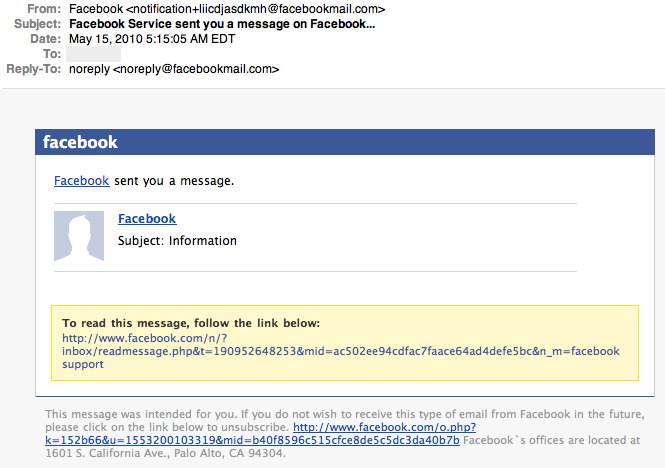
 Email filtering company Red Condor has been intercepting an email phishing campaign spreading faked Microsoft Outlook alerts at a phenomenal rate.
Email filtering company Red Condor has been intercepting an email phishing campaign spreading faked Microsoft Outlook alerts at a phenomenal rate.